Mục đích: Cấu hình router để kiểm tra các traffic hướng ra và tự động mở ra các ACCESS-LIST pinhole.
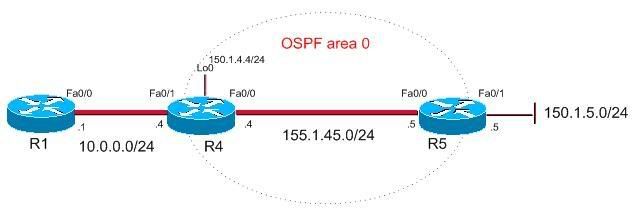
Mô hình:
Hướng dẫn:
Cấu hình tham khảo:
Bước 1: Cấu hình cơ bản: địa chỉ IP, định tuyến OSPF, NAT PAT
Router R4
interface Loopback0
ip address 150.1.4.4 255.255.255.0
!
interface FastEthernet0/0
ip address 155.1.45.4 255.255.255.0
ip nat outside
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 10.0.0.4 255.255.255.0
ip nat inside
duplex auto
speed auto
!
router ospf 1
log-adjacency-changes
network 150.1.4.0 0.0.0.255 area 0
network 155.1.45.0 0.0.0.255 area 0
!
ip classless
ip http server
ip nat inside source list 1 interface Loopback0 overload
!
access-list 1 permit 10.0.0.0 0.0.0.255
!
control-plane
!
!
line con 0
logging synchronous
line aux 0
line vty 0 4
login
Router R5
interface FastEthernet0/0
ip address 155.1.45.5 255.255.255.0
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 150.1.5.5 255.255.255.0
duplex auto
speed auto
no keepalive
!
router ospf 1
log-adjacency-changes
network 150.1.5.0 0.0.0.255 area 0
network 155.1.45.0 0.0.0.255 area 0
!
ip classless
!
!
ip http server
no ip http secure-server
!
control-plane
!
line con 0
line aux 0
line vty 0 4
privilege level 15
no login
Router R1
interface FastEthernet0/1
ip address 10.0.0.1 255.255.255.0
duplex auto
speed auto
!
ip classless
ip route 0.0.0.0 0.0.0.0 10.0.0.4
!
line con 0
line aux 0
line vty 0 4
privilege level 15
no login
Bước 2: Cấu hình access-list INBOUND và inspection rule INSPECT trên router R4
ip access-list extended INBOUND
permit ospf any any
deny ip any any log
!
ip inspect name INSPECT ftp
ip inspect name INSPECT icmp router-traffic
ip inspect name INSPECT tcp router-traffic
Apply access-list INBOUND (hướng in) và inspection rule INSPECT (hướng out) trên interface Fa0/0 của R4.
interface FastEthernet0/0
ip access-group INBOUND in
ip inspect INSPECT out
Bước 3: Kiểm tra
R4#sh ip inspect config
Session audit trail is disabled
Session alert is enabled
one-minute (sampling period) thresholds are [400:500] connections
max-incomplete sessions thresholds are [400:500]
max-incomplete tcp connections per host is 50. Block-time 0 minute.
tcp synwait-time is 30 sec -- tcp finwait-time is 5 sec
tcp idle-time is 3600 sec -- udp idle-time is 30 sec
dns-timeout is 5 sec
Inspection Rule Configuration
Inspection name INSPECT
ftp alert is on audit-trail is off timeout 3600
icmp alert is on audit-trail is off timeout 10
inspection of router local traffic is enabled
tcp alert is on audit-trail is off timeout 3600
inspection of router local traffic is enabled
R1#telnet 150.1.5.5
Trying 150.1.5.5 ... Open
R5>
R4#show ip inspect sessions
Established Sessions
Session 650FF88C (10.0.0.1:54327)=>(150.1.5.5:23) tcp SIS_OPEN
Session 650FFB04 (150.1.4.4:40087)=>(150.1.5.5:179) tcp SIS_OPEN
R4#ping 150.1.5.5
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 150.1.5.5, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 44/44/48 ms
R4#telnet 150.1.5.5
Trying 150.1.5.5 ... Open
R5>exit
[Connection to 150.1.5.5 closed by foreign host]
R5#conf t
Enter configuration commands, one per line. End with CNTL/Z.
R5(config)#ftp-server enable
R5(config)#ftp-server topdir flash:
R5(config)#do copy start flash:
Destination filename [r5-confg]? test.txt
Erase flash: before copying? [confirm]n
Verifying checksum... OK (0x10CB)
1668 bytes copied in 0.292 secs (5712 bytes/sec)
R1#copy ftp://150.1.5.5/test.txt null:
Accessing ftp://150.1.5.5/test.txt...
Loading test.txt !
[OK - 1668/4096 bytes]1668 bytes copied in 4.652 secs (359 bytes/sec)
-------------------------------------------------
Mô hình:
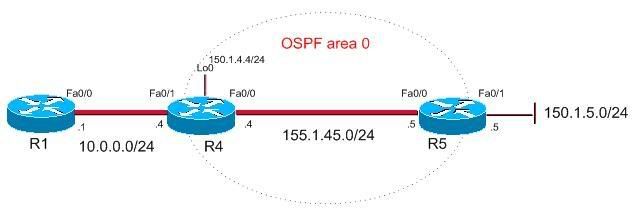
Hướng dẫn:
Cấu hình router (định tuyến, NAT, …) giống như bài LAB 2 ‘Lọc traffic với reflexive access-list’.
Tạo luật kiểm tra (inspection rule) tên là INSPECT để cho phép các giao thức dựa trên TCP.
Ngoài ra, cho phép FTP được thực hiện thông qua Firewall.
Tiếp theo, cấu hình luật này cho phép ICMP và kiểm tra các traffic TCP/ICMP do router tạo ra.
Tạo access-list INBOUND và cho phép OSPF. Chặn và ghi lại tất cả các traffic khác.
Apply access-list INBOUND trên cổng Fa0/0 theo hướng vào (in).
Apply luật kiểm tra trên cổng Fa0/0 theo hướng ra.
Tạo luật kiểm tra (inspection rule) tên là INSPECT để cho phép các giao thức dựa trên TCP.
Ngoài ra, cho phép FTP được thực hiện thông qua Firewall.
Tiếp theo, cấu hình luật này cho phép ICMP và kiểm tra các traffic TCP/ICMP do router tạo ra.
Tạo access-list INBOUND và cho phép OSPF. Chặn và ghi lại tất cả các traffic khác.
Apply access-list INBOUND trên cổng Fa0/0 theo hướng vào (in).
Apply luật kiểm tra trên cổng Fa0/0 theo hướng ra.
Cấu hình tham khảo:
Bước 1: Cấu hình cơ bản: địa chỉ IP, định tuyến OSPF, NAT PAT
Router R4
interface Loopback0
ip address 150.1.4.4 255.255.255.0
!
interface FastEthernet0/0
ip address 155.1.45.4 255.255.255.0
ip nat outside
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 10.0.0.4 255.255.255.0
ip nat inside
duplex auto
speed auto
!
router ospf 1
log-adjacency-changes
network 150.1.4.0 0.0.0.255 area 0
network 155.1.45.0 0.0.0.255 area 0
!
ip classless
ip http server
ip nat inside source list 1 interface Loopback0 overload
!
access-list 1 permit 10.0.0.0 0.0.0.255
!
control-plane
!
!
line con 0
logging synchronous
line aux 0
line vty 0 4
login
Router R5
interface FastEthernet0/0
ip address 155.1.45.5 255.255.255.0
duplex auto
speed auto
!
interface FastEthernet0/1
ip address 150.1.5.5 255.255.255.0
duplex auto
speed auto
no keepalive
!
router ospf 1
log-adjacency-changes
network 150.1.5.0 0.0.0.255 area 0
network 155.1.45.0 0.0.0.255 area 0
!
ip classless
!
!
ip http server
no ip http secure-server
!
control-plane
!
line con 0
line aux 0
line vty 0 4
privilege level 15
no login
Router R1
interface FastEthernet0/1
ip address 10.0.0.1 255.255.255.0
duplex auto
speed auto
!
ip classless
ip route 0.0.0.0 0.0.0.0 10.0.0.4
!
line con 0
line aux 0
line vty 0 4
privilege level 15
no login
Bước 2: Cấu hình access-list INBOUND và inspection rule INSPECT trên router R4
ip access-list extended INBOUND
permit ospf any any
deny ip any any log
!
ip inspect name INSPECT ftp
ip inspect name INSPECT icmp router-traffic
ip inspect name INSPECT tcp router-traffic
Apply access-list INBOUND (hướng in) và inspection rule INSPECT (hướng out) trên interface Fa0/0 của R4.
interface FastEthernet0/0
ip access-group INBOUND in
ip inspect INSPECT out
Bước 3: Kiểm tra
R4#sh ip inspect config
Session audit trail is disabled
Session alert is enabled
one-minute (sampling period) thresholds are [400:500] connections
max-incomplete sessions thresholds are [400:500]
max-incomplete tcp connections per host is 50. Block-time 0 minute.
tcp synwait-time is 30 sec -- tcp finwait-time is 5 sec
tcp idle-time is 3600 sec -- udp idle-time is 30 sec
dns-timeout is 5 sec
Inspection Rule Configuration
Inspection name INSPECT
ftp alert is on audit-trail is off timeout 3600
icmp alert is on audit-trail is off timeout 10
inspection of router local traffic is enabled
tcp alert is on audit-trail is off timeout 3600
inspection of router local traffic is enabled
R1#telnet 150.1.5.5
Trying 150.1.5.5 ... Open
R5>
R4#show ip inspect sessions
Established Sessions
Session 650FF88C (10.0.0.1:54327)=>(150.1.5.5:23) tcp SIS_OPEN
Session 650FFB04 (150.1.4.4:40087)=>(150.1.5.5:179) tcp SIS_OPEN
R4#ping 150.1.5.5
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 150.1.5.5, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 44/44/48 ms
R4#telnet 150.1.5.5
Trying 150.1.5.5 ... Open
R5>exit
[Connection to 150.1.5.5 closed by foreign host]
R5#conf t
Enter configuration commands, one per line. End with CNTL/Z.
R5(config)#ftp-server enable
R5(config)#ftp-server topdir flash:
R5(config)#do copy start flash:
Destination filename [r5-confg]? test.txt
Erase flash: before copying? [confirm]n
Verifying checksum... OK (0x10CB)
1668 bytes copied in 0.292 secs (5712 bytes/sec)
R1#copy ftp://150.1.5.5/test.txt null:
Accessing ftp://150.1.5.5/test.txt...
Loading test.txt !
[OK - 1668/4096 bytes]1668 bytes copied in 4.652 secs (359 bytes/sec)
-------------------------------------------------